Learn more about URIports
Read the most frequently asked questions about URIports and the answers. Also, check out our blog with more articles about DMARC, Content Security Policy, Network Error Logging (NEL), and more!
General
Once you've added the correct HTTP response headers to your website, your visitors' browsers are instructed to send reports to a configured address. When this address is set to your URIports account, we receive and process the reports so that in your account, you have a good overview of problems that occur on your website. Read more on our Getting Started page.
In addition to website reports, we can also receive and process DMARC, and MTA TLS reports. We receive them as soon as you have set the right policy in your DNS records. It sounds complicated, but it's not. Check out our Getting Started page for more info.
Our servers are located in the Netherlands (within the EU) and must comply with stringent privacy legislation. Furthermore, the servers are located in a highly secured data center to create the safest possible place for your data.
Most reports do not contain any personal information because the browsers and servers remove this data before submitting the reports. The only possible personal information present is the submitter's IP address, the browser's user agent, and the URL that triggered a 404 error, for example. We only need the IP address and user agent to connect specific reports to determine that a single visitor is responsible for multiple reports. We store a small part of a hash-based on (part of) the IP address and user agent combination, not the original data itself. If a report contains URLs, we remove any query parameters as well as email addresses.
DMARC failure reports may contain personal information. This is all filtered and removed before the reports are processed. We only store original failure report PGP encrypted when the user has supplied their public key.
Account and Billing
You can easily change your username/email address and the email address you would like to use to receive notifications. Go to settings and click the option to change your email address or click the notification settings.
Yes, of course, when your requirements change, you can always up or downgrade. Upgrades are instant, and you only pay the price difference between the old and new plan. In addition, we downgrade your subscription automatically after your old subscription expires.
We offer payment by invoice for companies based in the EU that would like to purchase an annual Mountain or Himalaya subscription.
Updating your contact details is quick and easy. You can do it directly on your invoice. Once updated, the changes will automatically apply to all future invoices. To view your latest invoice, log in to your account, click the user icon in the top-right corner, and then select "Settings". In the "Account" section, click the "Billing History" link to see your invoices. Open the latest invoice, where you'll have the option to modify your address. If you need to update your company VAT number or country, these changes need to be made through Paddle, our payment service provider. You can reach them at https://paddle.net. Be sure to have your latest invoice number handy when contacting them.
Contact us at our helpdesk and we'll arrange that for you.
You can cancel your subscription at any time. And whenever you do, the cancellation comes into effect on the expiration date of your current subscription. After that, we will not charge your payment method anymore. You can cancel your subscription from your account settings.
We're sorry to hear that you are leaving! You can close your account from your settings page. However, we will delete your account and related data immediately, and this action is not reversible.
We use Paddle as a platform to sell our subscription plans. They store your credit card details, and you receive your invoice from Paddle. Their name also appears on your billing statement. If you have any questions about a Paddle transaction, you can easily contact them.
If you find something that does not add up, send us a bug report at our helpdesk.
Thanks for your help! We will try to fix the bug as soon as possible.
You can easily hide report types you don't use. Go to your settings and click the "Hide report types" option.
Reporting
You certainly can! And you can search to find what you're looking for. Whatever the case, we already aggregate your data and sorted it so that the most important reports are at the top of the list. There are four easy ways to navigate your dataset:
Search: By searching you can easily find reports. Think of searching on a certain URL, a certain error code, or something else. Searches are performed directly across your entire data set.
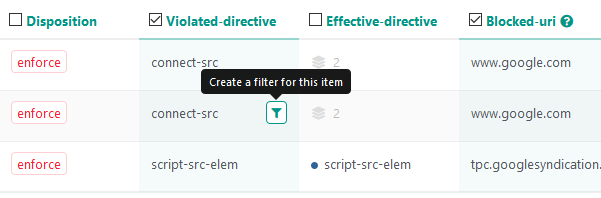
Filtering: You can easily filter for different dataset parts by clicking the filter icon next to the relevant field in your report.
View aggregated data: If an aggregated report contains multiple values in a specific field, we display it as an icon followed by a number ![]() . Click the icon to see the values. We then set a filter, so those are the exact values you see.
. Click the icon to see the values. We then set a filter, so those are the exact values you see.
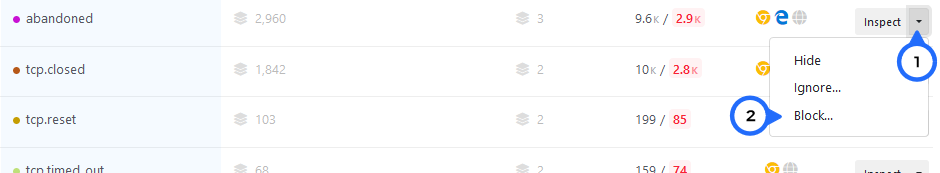
Inspect: If you want to view the individual reports in an aggregated dataset, you can click the "Inspect" button to the right of an aggregated report. This opens a window containing all the individual reports. Values that are unique to individual reports are summarized at the top of the window.
Reports many individual site visitors trigger are highlighted by a red number in your report list.
The threshold is based on the number of individual clients sharing the same violation relative to the total number of individual clients.
Reports that exceed the set threshold are the ones that you need to focus on. All website reports are automatically sorted based on this threshold, so you can immediately see what's important.
To ignore or block reports about issues you can't fix, you can set ignore and block rules in your account. Find out more by reading our blog about setting up ignore and block rules.
Yes, you can. Read our blog about setting up ignore and block rules.
When we receive a report that you would like to block, we don't process it in your account, and we drop it when we receive it. Blocked reports don't count towards your quota, but we use a fair use policy for blocking reports to keep our service running smoothly.
You can set up ignore and block rules in your account. To find out more, read our blog on the topic.
Ignored reports are processed like regular reports – the only difference is that ignored reports are automatically hidden from your standard report view. You can view hidden reports by flipping the "Show hidden" switch in the report view.
Blocked reports don't count towards your monthly quota, but we apply a fair use policy for blocking reports to ensure that our service runs smoothly. Blocked reports have to be processed by our system to check whether or not they have to be blocked. The current fair use policy is 20% of your quota. So if you have a subscription with 500,000 reports, you can block 100,000 reports every month. The fair use policy may change unannounced in the future. When you exceed the fair use policy limit, newly blocked reports may count towards your monthly quota. Unactionable violations, like the “abandoned” network error, are excluded from the fair use policy.
You have two options: you can either fix the violation or add the source to the allowlist. Read our blog about setting up a solid and secure Content Security Policy. It contains some tips and tricks on how to fix CSP violations.
Some violations cannot be fixed, and for those you can set ignore and block rules.
These network errors occur when someone visiting your site aborts fetching a resource before the action is complete. For example, this can happen when a user is navigating to another page on your site before the site is fully loaded or when an ajax call is aborted. Unfortunately, there is not much you can do to fix abandoned reports. However, you can block or ignore them when you don't want to see them in your account.
Notifications
You can define what type of notifications you would like to receive from different notification channels in your account settings. The email notification channel also has the option to set a notification frequency to aggregate notifications.
Yes, you can be notified immediately about site errors via our Telegram bot or a custom webhook connected to your own tools. All alerts are triggered by real issues experienced by your visitors.
DMARC
DMARC (Domain-based Message Authentication, Reporting, and Conformance) aggregate reports contain information about the authentication status of emails sent on behalf of a domain. With these reports, you can see which messages authenticate against DKIM and SPF standards. You can also see which emails do not authenticate.
An aggregated report does not contain information about the email itself but about the source that sent the message: the domain used when sending the IP address of the sending server, the number of messages sent on a given date, the DKIM and SPF sending domain and the authentication status.
All this information is helpful for checking who might be sending an email on your behalf, whether the sender is allowed to send an email on your behalf, and whether these messages are properly authenticating against DKIM and SPF standards. You can also check who is sending malicious emails on your behalf.
Ultimately, you can ensure that the malicious emails do not reach the recipient's inbox. You can do this by enforcing a DMARC rejection policy.
A DMARC failure report contains the original email and email headers for an email that has failed delivery because it did not pass the DMARC validation. These reports can be handy for analyzing why an email failed the DMARC validation. When we receive a report, we strip the message body and clean the headers of all privacy-sensitive information so our servers do not process any personal data.
It is possible to save the unfiltered headers by uploading your PGP public key. The email headers are then encrypted with your PGP public key. Read more about privacy and DMARC failure reports in our blog.
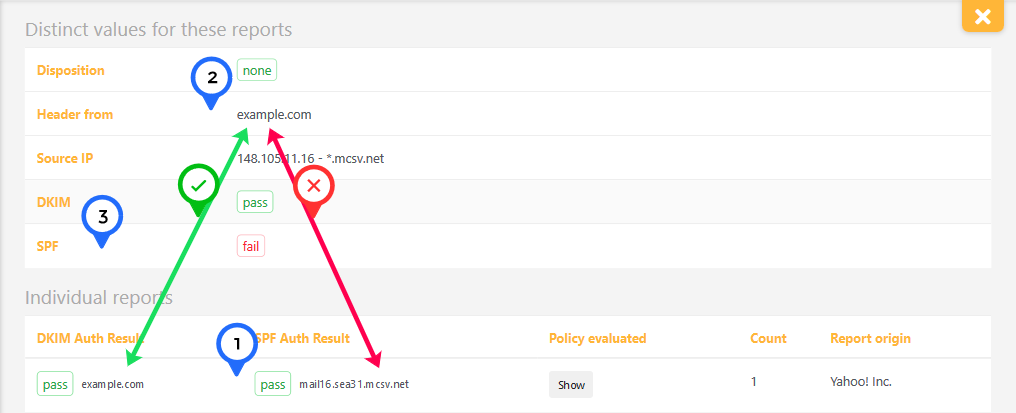
SPF and DKIM can associate pieces of an email with a domain. DMARC tries to match the results of SPF and DKIM with the content of the email and specifically with the domain found in the email headers like the "From:" header. There is an alignment if the domain in the email headers matches the SPF and DKIM domain. If there is an alignment, the email passes DMARC validation.
Have a look at the example below. The SPF auth results for hostname mail16.sea31.mcsv.net pass (1), but the hostname does not match the "Header from"-value example.com (2). This causes the DMARC SPF check to fail (3). Please keep in mind that for DMARC to fail, BOTH SPF and DKIM must generate anything other than pass. So in the example below, the message still passes the DMARC validation. SPF can fail when messages are forwarded or are sent from a third-party service. Avoid DMARC failures by adding a DKIM signature to every message sent on your domain's behalf.
When you publish your new DMARC policy in your DNS, it can take up to 72 hours for email providers to load it due to DNS caching. So, you should see results in your URIports account within 72 hours after updating your DNS records.
Besides this, it is good to know that most email providers send daily reports.
To ensure that you receive DMARC failure reports, you must create a DMARC record and publish it in the domain's DNS. After publishing a DMARC record, URIports can receive failure (forensic) DMARC reports from all ISPs that support DMARC. These reports contain crucial information to secure your domain. Check out our Getting Started page on how to configure your DMARC record in your DNS.
Bear in mind that only a fraction (< 5%) of servers that support DMARC send failure reports, primarily due to privacy concerns.
Simply put, DMARC compliance means that the emails you or your organization send all pass DMARC validation. The goal is to achieve the highest possible DMARC compliance so that no legitimate email is blocked.